Increasing your security and convenience by design.
One technology partner delivering a seamlessly integrated solution with cost-saving offline and online locks, mobile access, data-on-card, and cloud services.
Plug & Play for seamless adaptation.
From medium to enterprise-sized facilities we can provide a tailored fit for your business needs.
Main Value
01. Adaptable
- Users can have personalized menus that comply with GDPR rules and can also obtain login access rights based on their location.
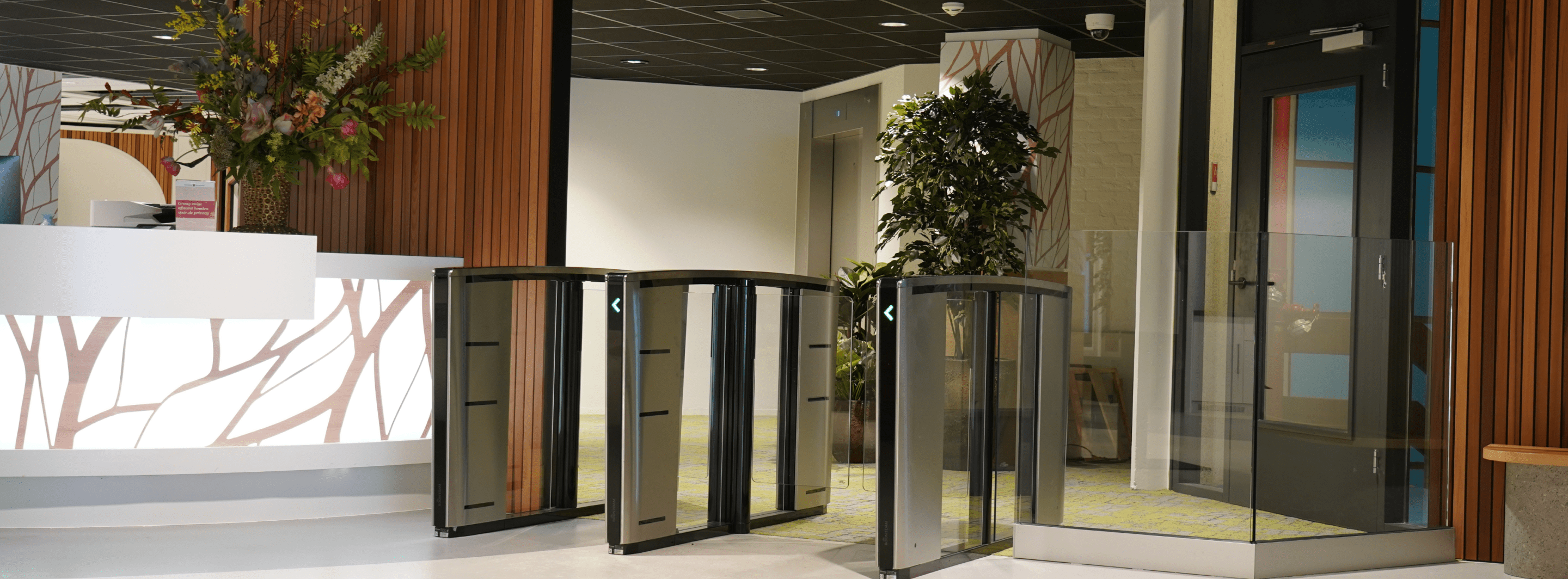
- Our system fully supports all combinations of electrical door locks, such as high-speed door gates, rolling grilles, turnstiles, and includes registration of the lock status.
- Works independently as one system when using multiple main brands of offline and online door handles, cylinders, and card readers.

02. User Experience Focused
- Manage and control a large number of locations from one or more central locations (multi-site).
- Based on your needs, you can define priority-based alarm handling including interactive floor plans.
- Customize a cockpit to your business needs with automatic event-driven layouts highlighting relevant information instantly.
- Multi-language capabilities within one system allow you to seamlessly communicate internally, without barriers.

03. A High Standard of Security
- End-to-end security – Protect your data against any cyberattacks with encrypted communication.
- Possibility to check and install daily updated security patches.
- Manage and update your hardware with the latest software versions automatically.
- We use open standards and community software to provide a consistently secure environment. PEN-tested according to OWASP method.

04. Reporting & Information Management
- Several possibilities for your reporting and data purposes.
- You can create a pre-selection report which can be executed directly from IPROTECT Cloud, e.g., Interactive floorplan.
- Create your own dashboard.
- Fully aligned with the GDPR.

Videos
Main Functionalities
Control Center
With events that can occur as a one-off, or simultaneously, it’s crucial to have an overview of what is happening and where.
The Solution
Alarm procedures are tailored to your individual needs, allowing you to assign a priority characteristic and follow-up action through a pop-up screen on the administrator’s workstation. Supported by an interactive floorplan and camera images, you can see ‘live’ what is going on and where whilst saving and reviewing these images afterward.
How can a Control Center functionality benefit my facility
- Alarm distribution: Option of different types of alarm procedures: security alarm, technical alarm, general alarm.
- Alarm actions: You can set which actions you want to combine, for example:
- Emergency response card authorization.
- Burglar alarm camera preferences & automatic door locking.
- Description prompt when alarm activated for situation overview.
- The guard knows exactly which action(s) must be performed before the alarm can be reset.
Offline, Online Access
Facilities require high-speed access to multiple passages, while also requiring locking mechanisms for less frequently used areas with different access requirements.
The Solution
Offline and Online Access locks cater to both scenarios in a facility, providing online access card readers for frequent use and offline electronic door locks with integrated readers and batteries for infrequent use, eliminating the need for cabling.
Why use Offline, Online Access?
- Provides heightened security in both online and offline areas through authorized and updatable access cards.
- Users do not have to differentiate between presenting their access card on an online or offline card reader.
- Combining online and offline card readers creates a secure and flexible closing plan.
- Access cards provide information on the status of offline electronic locks.
Mobile App
IPROTECT follows the core principle of “mobile is key” by supporting mobile devices. This applies to both using and creating/assigning rights to locks and individuals.
Access management
Access management to a building:
- One mobile app for our online readers and DOM locks for Android and iOS.
- Simplification of card handling process for access control systems which unburdens system administrators and end-users in both an operational and logistical way.
- No physical card management needed for mobile devices.
- Data on mobile – Access rights and events are sent directly to or from the mobile device.
- Heightened security of the building with your mobile as a key.
Setup and update management
Setup and update management of hardware such as locks and readers:
- Use mobile app to update locks.
- Possibility to seamlessly switch from offline to online locks in order to update them.
How it works
Mobile devices are part of our everyday lives, delivering convenient solutions to fit in with our movements and actions.
The Solution
Our app links with IPROTECT Cloud, turning your phone into a key using:
- Scan&Go – allows users to open doors by holding their device within range of the reader.
- Select&Go – The system shows nearby readers and pressing the selected reader’s button opens the door.
- Background Mode – allows access without unlocking the device or opening the app.
How can the mobile application benefit my facility?
- Easy registration – End-users are invited through IPROTECT to the system where they will receive an invitation email with a QR code to download the mobile app and register their organization.
- Flexibility – Per reader, users can customize their phone’s usage settings. This includes options such as requiring the phone to be unlocked prior to use, opening doors within a specified distance, or directly presenting the phone for specific tasks.
- Our app is multilanguage supported on Android and iOS.
- Storing multiple organizations – Supports multiple organizations, allowing for easier access to facilities for tenants or visitors traveling between different organizations.
Multi-Tenant Office
Managing access to individual office spaces or floors in a multi-tenant building can be challenging, particularly when multiple users are involved.
The Solution
Access Control helps property owners manage access for their tenants in a flexible and friendly way. Through distributed rights each tenant has the possibility to manage their visitors through this GDPR compliant system.
Why use Multi-Tenant solutions in my facility?
It allows you to:
- Streamline the process of access for users that run their own offices within the facility.
- Cut back on the complexity of trying to run a facility that caters to multiple different daily needs.
Multi-Credentials
Multi-tenant buildings need to accommodate varying access credential preferences for tenants and visitors without the need to switch to a new type of ID or credential.
The Solution
Multi-Credentials enables secure and flexible access for visitors and employees of different companies using various technologies such as QR codes, biometrics, mobile cards, MIFARE DESfire cards, and Bluetooth. The process for creating or deleting access in IPROTECT is the same, regardless of the credential used.
How can my facility benefit from Multi-Credentials?
- Provides tenants with flexibility and ease of choosing preferred access credentials.
- Enhances security and strengthens the entrance process.
- Enables granting, changing, or restricting access through Multi-Credentials when necessary.
Multilocations
Efficiently managing large facilities involves combining information from multiple systems, allowing you to optimize cost savings by overseeing various locations from a single control center.
The Solution
A single central coordinating server allows a system operator to manage multiple systems through a unified user interface, providing a comprehensive overview of ongoing situations through alarms, events, and interactive floorplans.
Why Multilocations?
Along with a better overview of security operations you can:
- Share access keys between multiple servers for efficient access control.
- Combine multi-site functionality with server synchronization.
- Save time whilst stepping up the security of your facilities.
- Save money and spread risks.
Trails – Authorization of User Group and PC Settings
Developing a system to dynamically assign user rights based on the workstation’s location is a common pain point.
The Solution
Our system adjusts user rights based on workstation and login locations, enabling control, accommodating employees in multiple locations or departments, and enhancing security measures.
Why do I need location restrictions?
- Tailor menu rights by assigning them based on the location and type of workstation.
- Login restriction (option) with person present in area to login.
Interactive Floorplans
How do you monitor security in an efficient way when it comes to one, or multiple facilities?
The Solution
Floorplans is an interactive platform that seamlessly integrates crucial daily use activities that can be tailored for each type of user with a number of possible options such as:
- Opening a predefined report.
- Live control and management of objects such as cameras and card readers.
- Area counters that help manage parking lot numbers.
- Opening a menu item.
- Viewing historical events of an object.
- Showing objects with a definable deviation.
Why Floorplans for my facility?
- Personalized menu and reporting.
- Monitor latest events.
- Interactive object (icons) with status.
- Arm/disarm your facilities alarm system.
- Adjust card reader status for example: Open/Closed/Automatic.
TKH TANlock
TKH TANlock offers an advanced electromechanical locking system specifically tailored for all areas which need to be secured such as data centers, or in your critical infrastructure.
The Solution
Managed by IPROTECT’s integration, it offers protection to sensitive equipment through enhanced security features – with all the benefits of a wired card reader.
Features
- Full integrated provisioning of rack handle settings, firmware, and keystore.
- Secure connection.
- Log events from the rack handle in IPROTECT including images of those accessing racks thanks to our Video Management System Integration – VDG SENSE.
- Local stored cards for calamity openings by lost network connection.
- Support of handle locked and door position input.
- Intrusion detection protecting the doors of the racks.
- Remote opening.
- Manage different access rights within one server room for different companies and server cabinets.
- Additional authentication with PIN code support.
- Support of FQDN (Full Qualified Domain Name).
Key Cabinet
In a multitude of environments and sectors, efficient key management for facility managers is essential, from universities and prisons, to corporations, hospitals, and more – where traditional methods often lack accountability.
The Solution
A key cabinet is a lockable cabinet containing individual RFID keyTags that can be provided with one or more physical keys, with access managed by presenting an access card to a connected reader – managed and controlled by our IPROTECT AC system.
Features
- Alarm Notification: The system sends a notification when a keyTag is not returned in time, preventing unauthorized access and reinforcing security protocols.
- Track Whereabouts: Provides an overview of the removal and reinsertion of keyTags, including person information and time stamps.
- Access Control Integration: Prevent people from leaving a certain area if they still possess keyTags – all linked to the corresponding card number.
- Keymap Functionality: IPROTECT’s intuitive keymap feature offers an overview of the cabinet, providing instant status updates on keyTag availability.
User Management: IPROTECT simplifies user categorization into Administration or Daily User roles, facilitating control over access rights and time zone settings for keyTag usage.
Pager Management System
Effectiveness is important to prevent many ‘expensive’ pagers from remaining unused in the charging station.
The Solution
By presenting an access card, an available pager is loaded with the user’s profile.
Why do I need IPROTECT to manage my Pager Management System?
- The number of pagers in use is optimized as much as possible.
- Pager number and profile managed by IPROTECT.
- Pager requests logged in IPROTECT.
Parking Management
Tracking resident and visitor entrants in shared parking areas enhances the efficiency of multi-tenant premises.
The Solution
This functionality allows operators to define the number of spaces for vehicles, carefully allocated for each business within your premises.
Why use Parking Management for my facility?
- Define quota or ‘blocks’ of spaces to registered visitors using passes.
- Count the number of vehicles currently parked using entry and exit tracking.
- Reject tenant parking when max allocation has been reached.
- Switch parking lots between tenants and implement a streamlined end-of-month billing system for convenience and flexibility.
Threat Management Level
Situations change daily and the threat management level of your facility needs to be appropriately set for different times.
The Solution
With Threat Management Level, functionalities can be adjusted when the situation is appropriate.
For example:
- Whether or not to use a pin code.
- Changing normal access to remote access through the intervention of a control room (video verification).
- Being able to block certain groups of people, for example, visitors.
Why do I need to consider the Threat Management Level of my facility?
Facilities can have a systematic and controlled approach to stay on top of potential threats in many different forms, requiring constant monitoring.
Push Transaction Extended
Send events to another system, with options to customize the event type and content.
The Solution
With the JSON push transaction webservice it is possible to send IPROTECT transactions in JSON format to an external system like an “Elastic Stack”. It is possible to specify precisely which transactions are sent and what data is added.
What is the benefit of Push transaction?
- By defining the event types and their relevant data to be sent, only necessary information is stored.
- End user is independent in choosing database type for storage events.
- End user is independent when making a choice of type of tooling for making overviews/reports.
Anti Passback Functionality
Leaving or returning to an area can pose security issues, such as visitors sharing passes, users attempting re-entry, and exceeding time limits.
The Solution
IPROTECT streamlines facility management by offering different security features for access control.
How does it work?
- APB: Refuses access when a person tries to enter an area (door) when the registered person is already inside.
- TAPB: Access is denied when a person tries to enter an area again within a certain time.
- TAPB Reversed: Access is denied when a person exceeds a time limit in a location making leaving the area not possible.
Two Man Rule
The two-man rule is a solution designed to achieve a high level of security for operations and actions that require two or more authorized persons at all times.
The Solution
An alarm will sound if the two-person requirement is not met, either due to unaccompanied visitors or insufficient personnel in the area.
Why consider a Two Man Rule?
- Within a facility, different areas can have different authorization levels.
- In some areas, two authorized persons must always be present.
- Certain visitors must be accompanied by authorized persons when they want to enter the area.
Interlocking
A secure, productive, and efficient method for opening and closing doors is critical for your facility’s controlled atmosphere, clean rooms, or heightened security solution.
The Solution
Interlocking is a highly effective security measure that ensures only one of multiple doors is open at a time. It provides secure access control and sends a ‘wait’ signal, allowing the door to be opened only when the other one is closed.
Why Interlocking for my facility?
- Secure and controlled access to areas.
- Controlled conditions when operating with atmospheric challenges.
- Detection and identification in secure areas.
- Preventing tailgating of unauthorized visitors.
Guard Tour
The importance of guard control rounds cannot be understated for building security, especially in security-sensitive areas where proper planning of rounds and routes is crucial.
The Solution
Guard Tour allows guards to walk pre-determined control rounds within a certain time during their shift with multiple predefined routes that can be set to your facility preferences.
What benefit will Guard Tour bring to my business?
- Register reporting point times via card readers, with minimum and maximum times.
- Receive automatic alarms for deviations, prompting swift action.
- Efficiently monitor predetermined areas with heightened awareness.
Trails – Walk Route
In monitored premises, tracking and controlling every movement is impossible. Yet, knowing the movements and routes of visitors and employees is essential.
The Solution
Walk Route allows a person to walk from A to B while the system checks if they follow the specified walking route within a certain time. The system will sound an alarm if there are any deviations.
Why do I need Walk Route?
- Define a route for visitors/employees.
- Strict control over access areas.
- With one button, you can pause all walking routes, simplifying operational management.